Managing Environment Files
One of the usefull things Laravel has done is introducing me to environment files, this is a concept that seems obvious now and was probably obvious years ago when working with other languages or even frameworks but it was something I hadn't come across before.
I have used Laravel Envoyer ever since it came out and this has a nice way of managing environment files, it allows them to be easily created and managed through the application.
For my work with Vestd I have been working on moving hosting over to AWS and eliminating potential security vulnerabilities such as Envoyer or Forge and generally setting up a more robust and reliable hosting environment. The downside of moving away from Envoyer is that you loose some of the nice features it has built in, and this brings me onto the point of this post, managing environment files.
I needed to replace Envoyer's management of env files so I decided to build a simple web app, the whole thing is really simple and should be simple to use but I needed to make sure it was safe and secure and kept accurate records of who did what.
I had been reading about Amazon's KMS service so I had it in mind that I wanted to make use of this, I also needed a secure way to get the environment files to the build server so they could be included in the web app being built. In the end I chose to encrypt the environment files using KMS and to store the encrypted data in the db, this data would be supplied in an encrypted form to the build server which would then decrypt and save the result as an environment file. This meant that I could use IAM policies to ensure that only those with permission could decode the encrypted data.
When designing the system I toyed with various ways of getting the data from the env manager to the build server in a secure way and in the end using KMS allows me to do this really easily, the encrypted data is made available to anyone who asks, only if they have permission within the AWS environment can they decode it.
The login system is tied to our Github org so managing access is done through Github's interface, this is a method I used with great success when building process monitor as it means one less things to maintain.
The final system is really basic and yet works well for the purpose, there are lots of different ways this could have been done but for now I am happy with the solution.
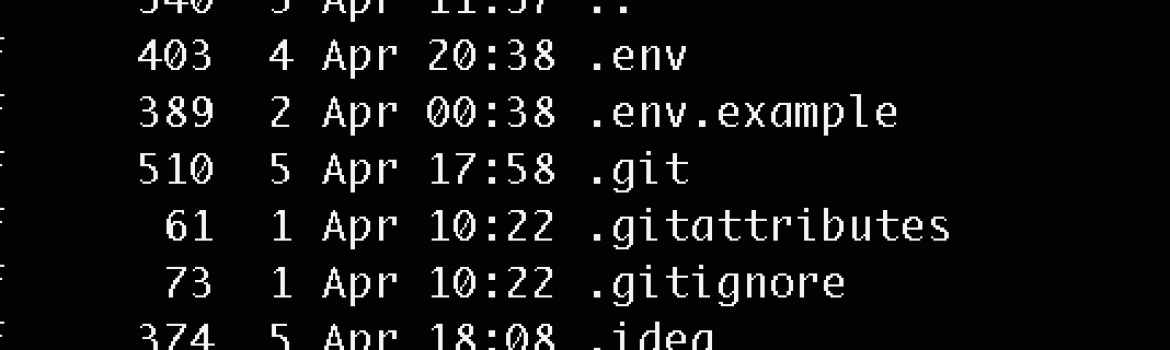
The env manager project is up on GitHub and available for anyone to use, its basic but may help someone in the same situation.